What is the #1 concern about vertical integration in industrial automation? You guessed it: security. We here at PI encourage you to work with your IT department because these guys have a lot to offer. They have lots of experience with security and we can draw from this experience as we start integrating IT and OT networks.
Security Priorities
But, we need to have an understanding on priorities, because in the IT world, Confidentiality is paramount followed by Integrity and Availability. In the OT world, these priorities are flipped. In OT, availability is paramount because we need to ensure controllers can perform real-time data exchange to keep the factory operating. Then we are concerned with Integrity and finally Confidentiality.
Defense in Depth
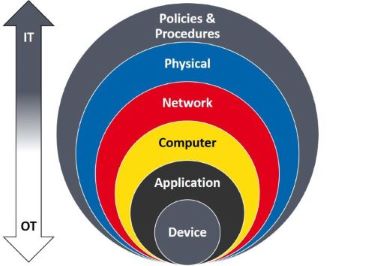 Even if there is disagreement with this shift in priorities, the one thing we can all agree on, no matter what side of the aisle you are on, is the concept of Defense in Depth. This is a concept where we look at the network holistically and build layers of security, like the layers of an onion, so if a malicious actor gets through one layer, there is another layer to provide the next level of protection. And then another layer, and another layer, and so on. From a network perspective it looks like the diagram on the right.
Even if there is disagreement with this shift in priorities, the one thing we can all agree on, no matter what side of the aisle you are on, is the concept of Defense in Depth. This is a concept where we look at the network holistically and build layers of security, like the layers of an onion, so if a malicious actor gets through one layer, there is another layer to provide the next level of protection. And then another layer, and another layer, and so on. From a network perspective it looks like the diagram on the right.
It all starts at the outer layer with Policies & Procedures where we establish who has access to what, and we control how maintenance and updates are handled. Then, we have the Physical security where we can have something as simple as putting locks on critical areas. Next is Network security where we can use things like network segmentation and key management to ensure devices are authorized to be on the network. We can add firewalls that allow access based on a configured set of rules, or make use of DMZs or data diodes. For those unfamiliar with DMZs, these prevent direct data access. Data must first be put in a neutral location and then it can be retrieved by the other side. There also are industrial firewalls available today that are intended for OT networks – meaning they are ruggedized, have a graphical user interface, and provide simplified administration tools that can be used by control engineers. As we move down into the Computer, Application, and Device layers, we find security tailored more toward OT networks where availability is the priority. And this is where PROFINET comes in.
Netload Test
Up until now, our current approach at PI has been to recommend a Defense in Depth strategy, and, on top of that, we require that every device passing through the test lab for certification to undergo a so called “Netload Test”. This is where we subject the device to a flood of network traffic to simulate a Denial of Service attack and make sure that the device not only degrades gracefully, but recovers automatically.
Security Classes
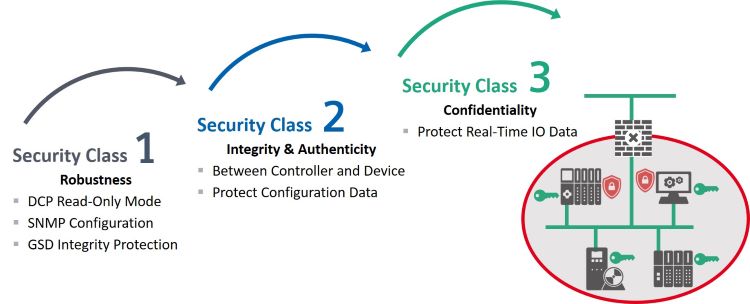
But now, the market is calling for additional levels of security, so we are looking beyond Netload and have come up with 3 security classes that are scalable.
- Class 1 is where we tighten up security for the DCP & SNMP protocols, and protect GSD files.
- Class 2 is where we use authenticity between a controller and a device to ensure a device is allowed to be on the network. This helps prevent man-in-the-middle attacks.
- Class 3 is where we are actually encrypting the real-time I/O data in case you are concerned it contains sensitive information like recipes, formulas, or other trade secrets.
Here is a simplified view of these additional security classes.
Again, these security classes are scalable with Class 1 starting to come on-line in the next year or so, then Class 2 and 3 will follow further on down the line. If you are interested in additional details regarding security and PI’s security classes starting with Security Class 1, please read this PROFINET Security Guideline, and , of course, contact us any time here at PI North America.
